Why Your GRC Tool is a Security Risk (The Data Sovereignty Problem)
-
 Balachandran Sivakumar
Balachandran Sivakumar - 11 May, 2026
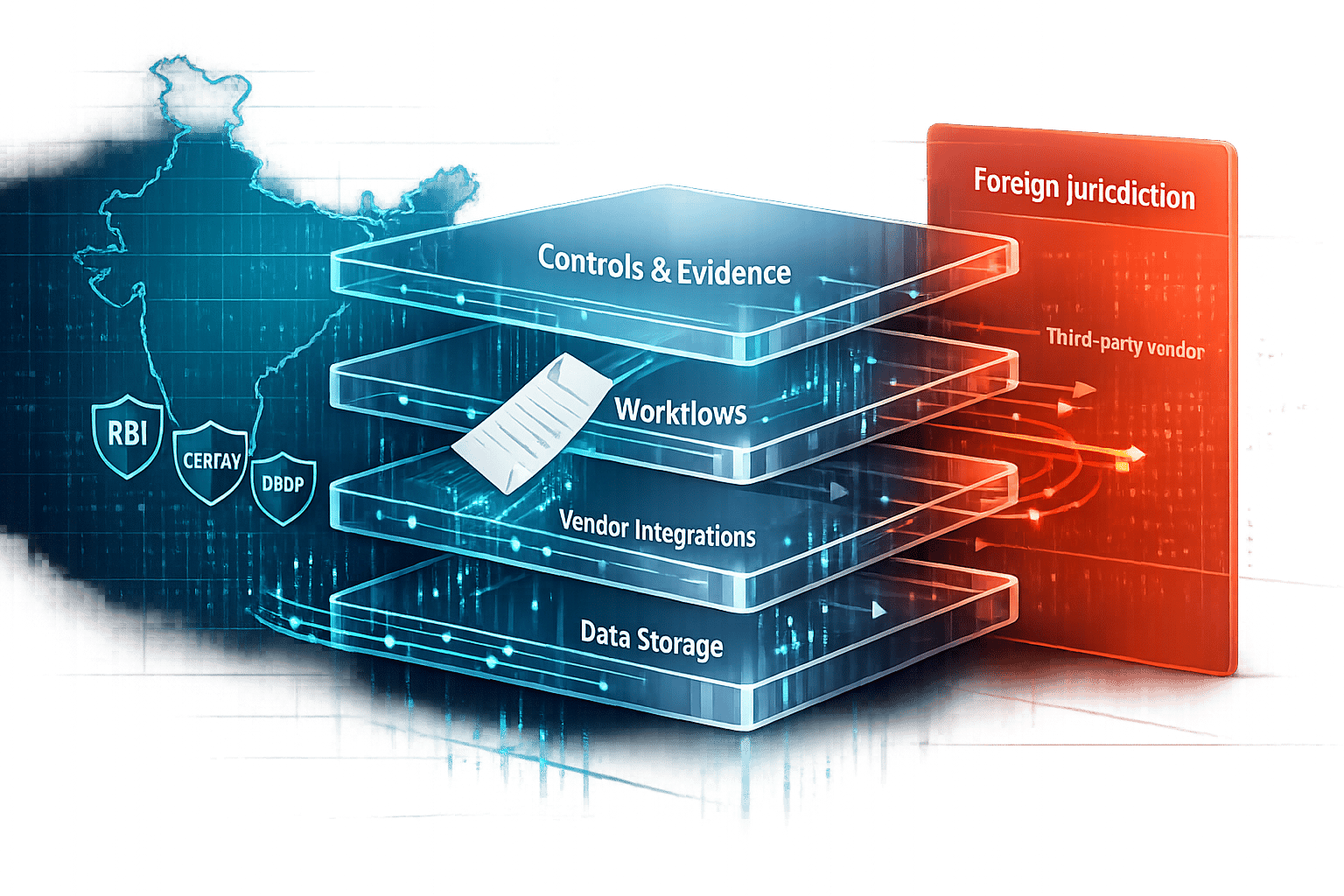
Your GRC tool might be creating security and compliance risks instead of solving them. For Indian businesses, regulations like RBI’s data localisation rules, CERT-In’s 6-hour incident reporting mandate, and the DPDP Act’s ₹250 crore penalties make compliance more challenging. Many GRC tools fail to address these complexities, especially when it comes to data sovereignty - who controls your data and under which jurisdiction.
Key Takeaways
- Data Sovereignty Misconceptions: Local data storage doesn’t guarantee compliance if foreign laws like the U.S. CLOUD Act apply.
- Manual Processes Increase Risk: Moving sensitive data manually during audits can lead to compliance gaps and exposure.
- Fragmented Systems: Incomplete vendor oversight and outdated tools make managing cross-border data flows almost impossible.
- Rising Penalties: GDPR fines hit €2.3 billion in 2025, and India’s DPDP Act allows fines up to ₹250 crore.
To fix this, companies need modern, AI-driven GRC platforms that automate compliance, ensure local data control, and provide real-time audit readiness.
How Traditional GRC Tools Create Data Sovereignty Risks
Traditional GRC tools often fall short when it comes to managing data sovereignty, leading to compliance gaps and potential security vulnerabilities.
Storing Data in Non-Compliant Regions
Many GRC vendors store compliance data in locations like Mumbai. However, if the provider is U.S.-based, it may still be subject to U.S. legal access requests regardless of where the data physically resides.
Indian organisations face this directly. The RBI requires payment system data to remain in India, and data processed abroad must be deleted from overseas systems within strict timelines. Legacy GRC platforms often cannot enforce this technically.
Manual Evidence Handling Exposes Data
Collecting evidence manually through spreadsheets, emails, and screenshots spreads sensitive information across insecure channels. Teams lose control over where data is stored, who accessed it, and whether it remains compliant.
This problem becomes worse when teams rush to meet reporting deadlines and rely on disconnected tools.
Fragmented Systems Increase Third-Party Risks
Traditional GRC systems often provide poor visibility into third-party and sub-processor chains. That makes it difficult to track where data moves across borders and whether vendor controls remain compliant.
Without automated data-flow mapping and continuous control monitoring, organisations cannot prove compliance when regulators ask for evidence.
The Real Cost of Ignoring Data Sovereignty in GRC
Overlooking data sovereignty in GRC leads to regulatory exposure, certification delays, and high operational costs.
Certification Delays and Regulatory Penalties
Indian organisations face overlapping obligations under RBI directives, CERT-In incident timelines, and the DPDP Act. Non-compliance can trigger severe penalties, including fines up to ₹250 crore.
Globally, enforcement is accelerating. GDPR penalties reached €2.3 billion in 2025, with continued year-over-year growth.
Managing Compliance Across Multiple Frameworks
Most organisations must satisfy multiple frameworks simultaneously - ISO 27001, SOC 2, GDPR, and local mandates. The challenge is not only policy mapping but proving technical controls such as encryption ownership, backup locations, and legal jurisdiction.
Manual, spreadsheet-based workflows struggle to maintain this evidence consistently.
How Manual Workflows Increase Risk and Slow Compliance
Manual processes widen the gap between policy intent and technical enforcement. They also fail to track secondary data flows like logs, diagnostics, AI metadata, and cloud backups.
As a result, teams are often reactive during audits and incident events rather than continuously prepared.
How to Fix Data Sovereignty Problems in Your GRC Program
Step 1: Assess Your Data Sovereignty Gaps
Run a full data mapping exercise. Identify data location, legal jurisdiction exposure, and cross-border movement paths including vendors and sub-processors.
Classify data by risk (low, medium, high), and enforce India-only handling for high-risk categories.
Step 2: Deploy AI-Driven GRC Platforms
Use an AI-powered platform to continuously monitor data movement and control compliance. Apply policy-as-code to enforce jurisdiction rules in real time.
Step 3: Automate Evidence Collection and Monitoring
Automate evidence collection for control performance, residency enforcement, and incident response timelines. This is essential for strict requirements like CERT-In reporting and long retention windows.
Step 4: Add Vendor Risk Management
Continuously monitor vendor and sub-processor changes. Detect hidden cross-border dependencies before they create regulatory exposure.
Step 5: Use Real-Time Dashboards for Audit Readiness
Move from static reports to live dashboards showing residency posture, control status, and evidence completeness across frameworks.
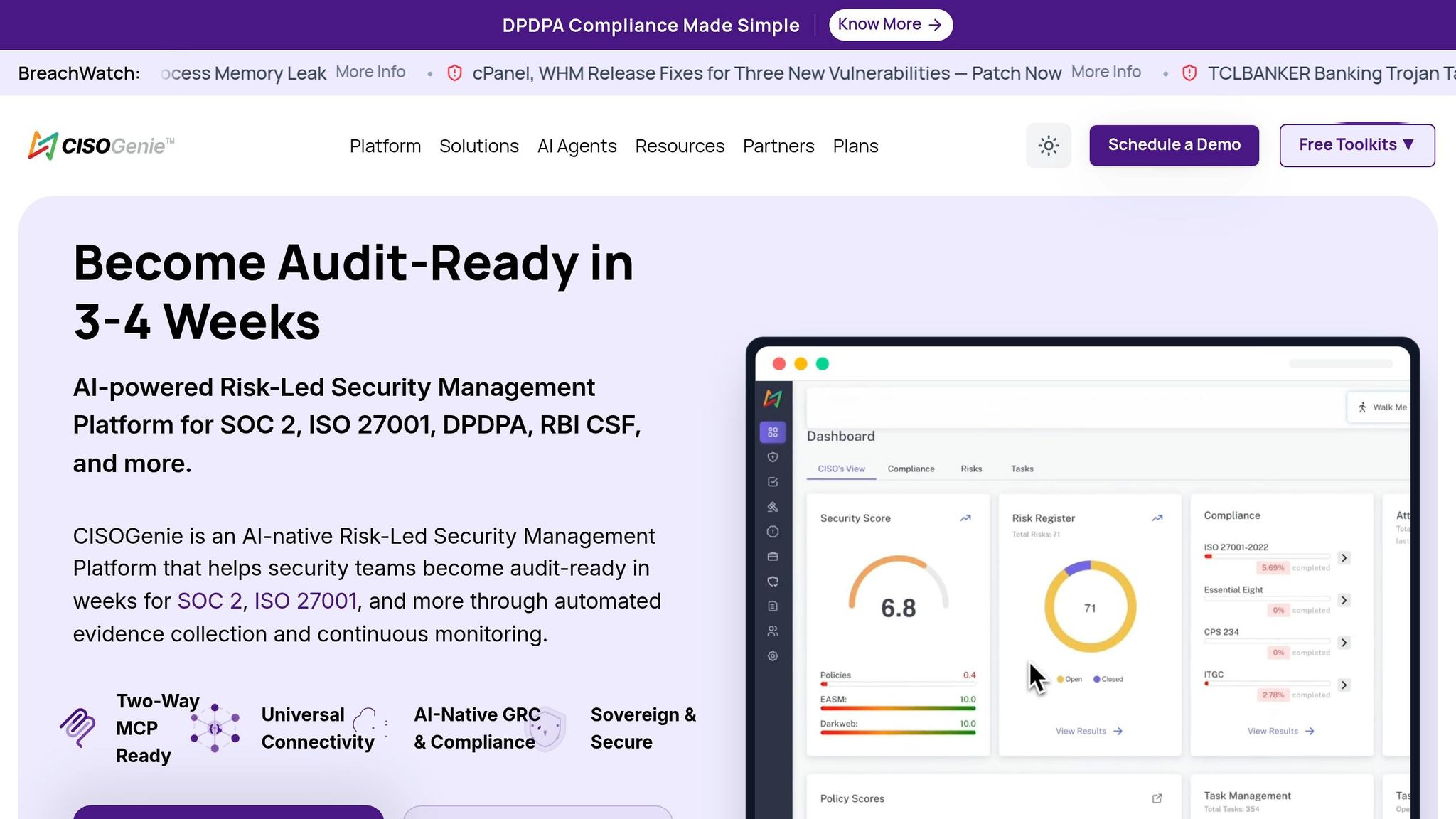
How CISOGenie Solves the Data Sovereignty Challenge
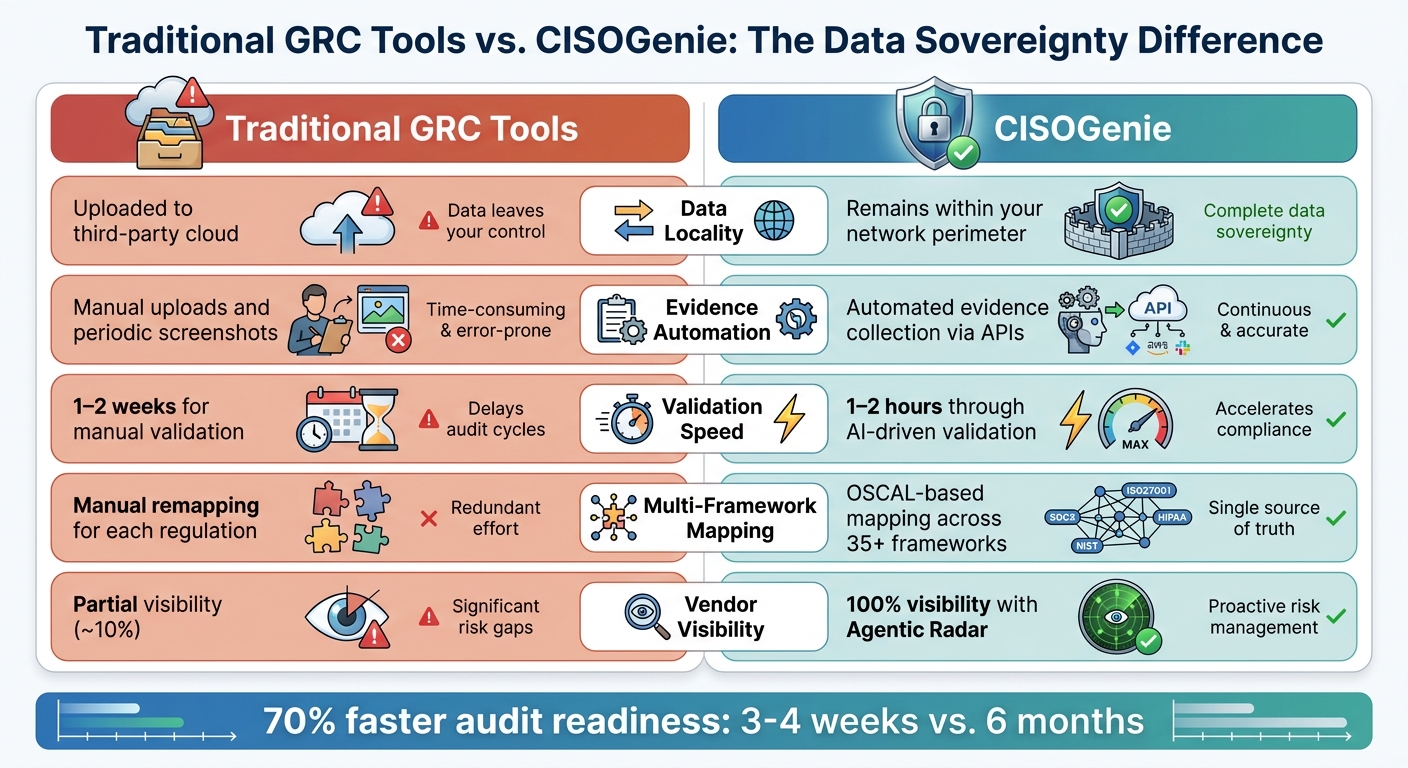
Traditional GRC Tools vs Modern AI-Powered GRC Platforms Comparison
AI-Powered Compliance Automation
CISOGenie uses AI agents for evidence collection, policy validation, and risk analysis while keeping operations within your environment. It supports 35+ frameworks and uses OSCAL-based control mapping to reduce remapping effort.
Zero Trust Architecture for Data Sovereignty
Unlike tools that require data and credentials in third-party clouds, CISOGenie executes compliance operations inside your perimeter. This reduces sovereignty risk and improves control over encryption keys and evidence access.
Traditional GRC Tools vs. CISOGenie
| Feature | Traditional Tools | CISOGenie |
|---|---|---|
| Data Locality | Uploaded to third-party cloud | Remains within your network perimeter |
| Evidence Automation | Manual uploads and screenshots | Automated API-driven evidence collection |
| Validation Speed | 1–2 weeks | 1–2 hours |
| Multi-Framework Mapping | Manual remapping | OSCAL-based reuse across 35+ frameworks |
| Vendor Visibility | Partial visibility | End-to-end visibility |
Conclusion: Achieving Compliance Through Sovereignty-Aware GRC
Traditional GRC tools can become a security liability when they rely on manual evidence, fragmented tooling, and external cloud dependencies. For organisations dealing with RBI, CERT-In, DPDP, and global requirements, sovereignty-aware automation is no longer optional.
AI-powered platforms that combine internal execution, continuous monitoring, and machine-readable compliance controls provide a practical path to faster, safer, and auditable compliance.
FAQs
How do I prove data sovereignty beyond just “hosted in India”?
You need more than local hosting. Prove legal control, key ownership, access governance, and auditable enforcement of residency policies through logs and control evidence.
What’s the fastest way to stop manual evidence sharing during audits?
Adopt an AI-driven evidence automation platform that continuously collects and validates control evidence from source systems without manual uploads.
How can we track sub-processors and hidden cross-border data flows?
Implement continuous vendor and data-flow monitoring with automated mapping of third-party dependencies, backup routes, and cross-region processing paths.